This repository contains the implementation of a Secure Electronic Voting System leveraging advanced cryptographic techniques to ensure privacy, security, and transparency. The system is based on a multi-authority election scheme and incorporates features such as homomorphic encryption, digital signatures, and threshold decryption for a robust voting process.
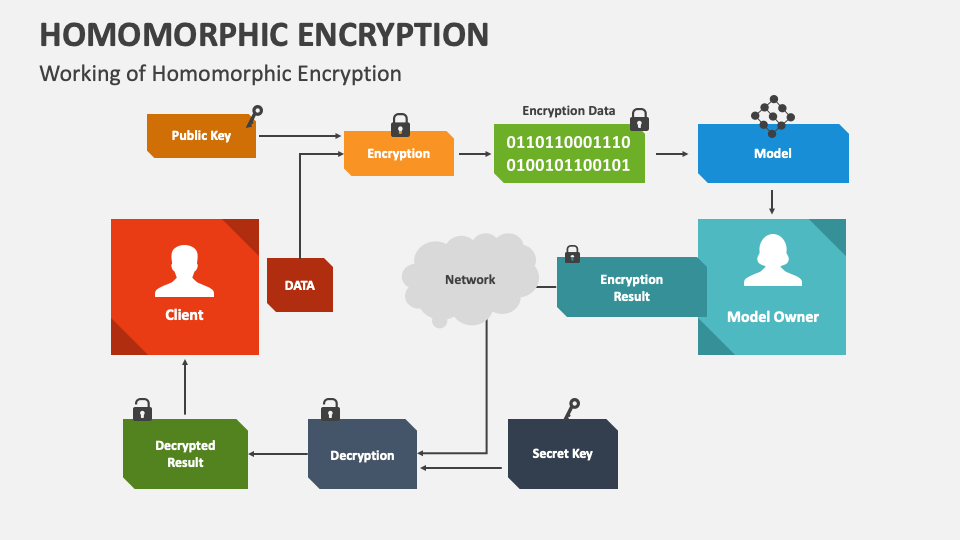
- Each voter encrypts their choice (e.g., Yes/No) using a homomorphic encryption algorithm.
- The encryption guarantees that the tally of votes can be computed without decrypting individual votes, ensuring vote secrecy.
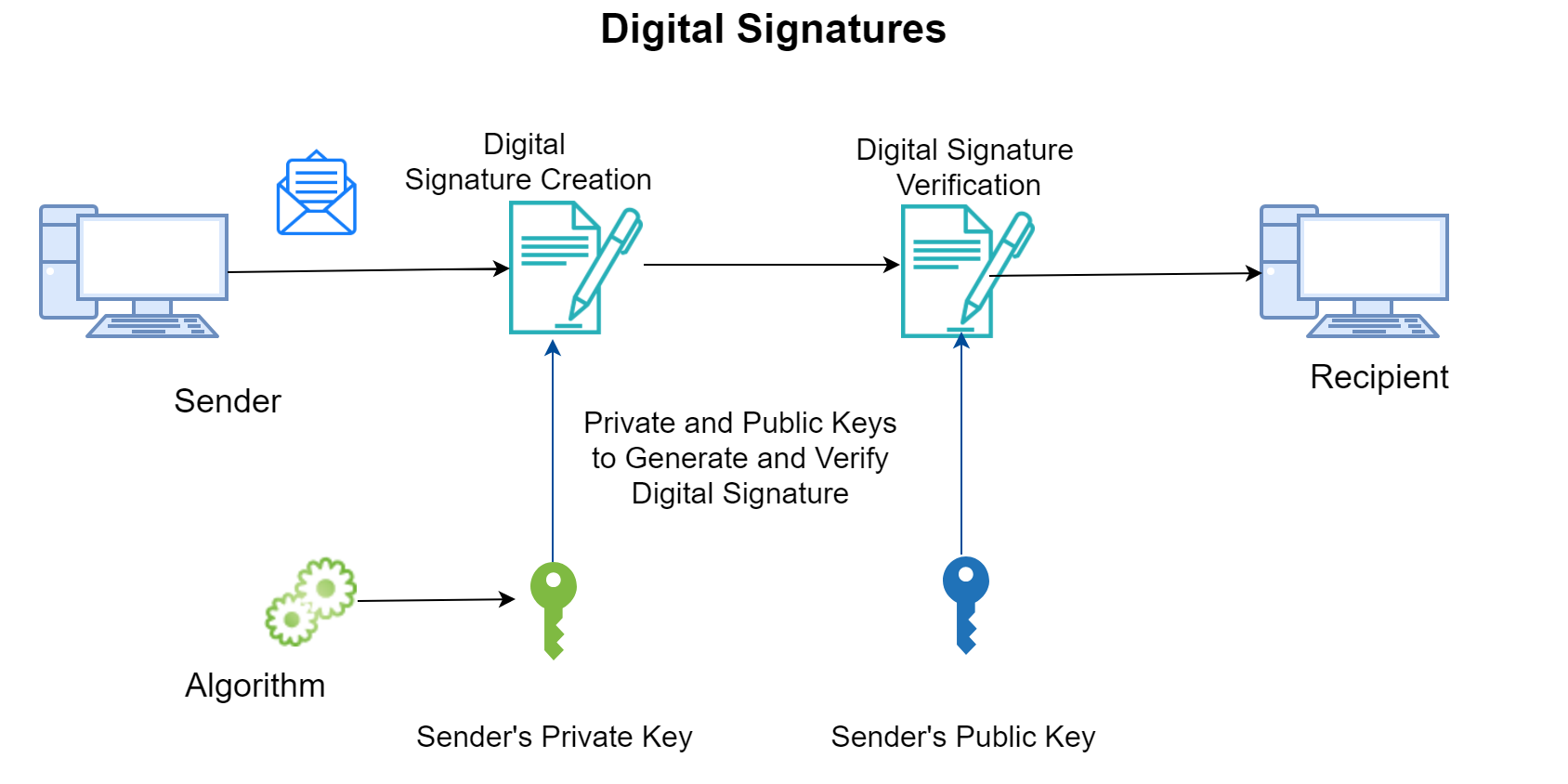
- Voters sign the cryptogram (encrypted vote) using digital signatures.
- This signature proves that the vote originates from an authorized voter, maintaining the system's integrity.
- To mitigate risks of vote decryption by a dishonest authority, the decryption key is distributed across multiple parties using a Shamir (t, n)-threshold scheme.
- At least
tout ofnparties must collaborate to reveal the vote tally, ensuring no single authority can compromise the system.
- Initially, a trusted center is assumed to set up the system by choosing necessary cryptographic parameters (e.g., primes
pandq). - However, the system can also operate without a trusted center by employing a secure communication protocol executed by the parties involved.
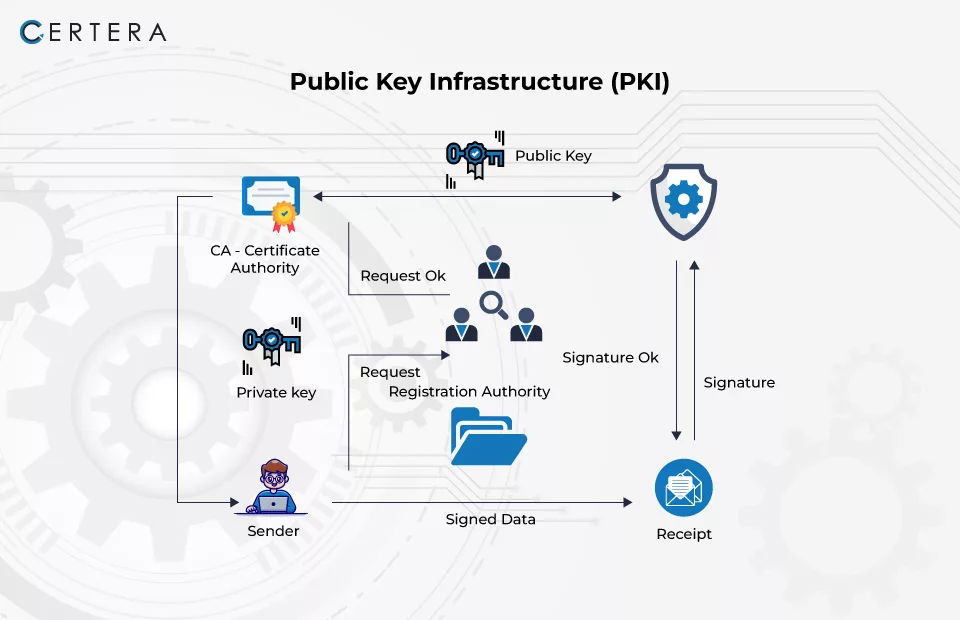
- A public-key infrastructure (PKI) is used to authenticate messages and guarantee the origin of all posted data.
- This ensures that only legitimate participants can interact with the system.
- The system uses a bulletin board as a shared, publicly accessible memory for posting encrypted votes and related cryptographic data.
- The bulletin board allows transparency and verifiability:
- Every member has a designated section to post messages.
- No one can delete or modify any information once posted.
- The complete board is viewable by all members, including external observers.
-
Voter Registration
Each voter receives a cryptographic key pair for encryption and digital signatures. -
Vote Casting
- The voter encrypts their choice using homomorphic encryption.
- The encrypted vote is signed and posted to the bulletin board.
-
Vote Collection
- All encrypted votes are stored on the bulletin board.
- Votes remain confidential as they are not decrypted during this stage.
-
Tallying
- The authorities compute the tally directly on the encrypted votes.
- Decryption is performed collaboratively by at least
tout ofnauthorities, ensuring security.
- Privacy: Individual votes remain confidential throughout the process.
- Security: Threshold decryption prevents any single authority from compromising the system.
- Transparency: The bulletin board model allows public verifiability of the election process.
- Efficiency: The system is optimized for low time and communication complexity.
- Cryptography: Homomorphic Encryption, Digital Signatures, Shamir Threshold Scheme.
- Public-Key Infrastructure (PKI): For message authentication.
- Distributed Systems: Multi-authority setup for decentralized decryption.
- Replace the trusted center with a decentralized protocol for setting up cryptographic parameters.
- Optimize the communication model for larger-scale elections.
- Implement advanced user interfaces for ease of use by voters and authorities.
This system is based on the theoretical framework introduced in the research paper by [CraGenSch97], which outlines the secure multi-authority election scheme.